About
Our Goal
The Human-Centered Cybersecurity program within the NIST Visualization and Usability Group provides research evidence and guidance to policymakers, system engineers, organizational decision makers, and cybersecurity professionals so that they can make better decisions that consider the human element, thereby advancing cybersecurity adoption and empowering people to be active, informed partners in cybersecurity.
Ideally, this guidance should: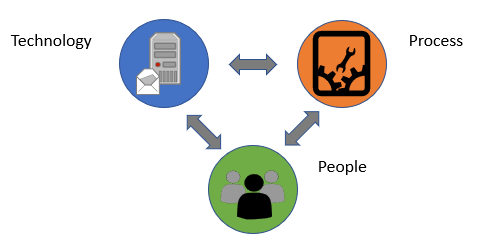
- Have a basis in real empirical data
- Create solutions that are secure in practice, not just in theory
- Take stakeholders' needs and behaviors into account
- Create an environment in which people feel empowered and engaged in cybersecurity
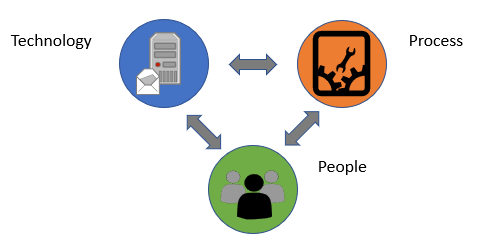
- Address the relationship between people, process, and technology factors
Interdisciplinary Approach
Usability, human factors, and cybersecurity are context-specific and influenced by a number of factors, such as the nature of the user population, organizational mission, and the specifications of the organization’s systems and cybersecurity measures themselves. Therefore, human-centered cybersecurity research requires an interdisciplinary approach. To that end, our team consists of experts in multiple fields, including cybersecurity, computer science, human factors, human-computer interaction, cognitive science, and psychology.